en2
Newbie level 1
Greetings,
Im currently trying to fix a strange behavior of objcopy, which sometimes generates invalid output binary image with 0x4 byte shift.
I found this issue because this shift was affecting my __init_array_start__ table (which is indeed pointing to right address in *.axf file, but after shift in binary file, its payload is gets corrupted - 1 pointer is 0x4 before desired table, and last item becomes null) - hard debugging week unfortunately
Here are the dumps produced by readelf and xxd:
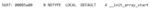
Orginal __init_array_start__ symbol from *.axf file (symbol point to 0x00085a80)
https://ibb.co/q75t9x4
Valid code payload from *.axf file (note that first entry is at correct 0x00085a80 address)

https://ibb.co/wQ93JCd
Invalid payload from *.bin file (note that first entry is at invalid 0x00085a7c address)

https://ibb.co/vdxS2H3
Im converting *.axf to *.bin with:
Is it a bug, or im missing something ?
Best,
Ernest
Im currently trying to fix a strange behavior of objcopy, which sometimes generates invalid output binary image with 0x4 byte shift.
I found this issue because this shift was affecting my __init_array_start__ table (which is indeed pointing to right address in *.axf file, but after shift in binary file, its payload is gets corrupted - 1 pointer is 0x4 before desired table, and last item becomes null) - hard debugging week unfortunately
Here are the dumps produced by readelf and xxd:
Orginal __init_array_start__ symbol from *.axf file (symbol point to 0x00085a80)
https://ibb.co/q75t9x4
Valid code payload from *.axf file (note that first entry is at correct 0x00085a80 address)
https://ibb.co/wQ93JCd
Invalid payload from *.bin file (note that first entry is at invalid 0x00085a7c address)
https://ibb.co/vdxS2H3
Im converting *.axf to *.bin with:
Code:
arm-none-eabi-objcopy -O binary binary/executable.axf binary/executable.binBest,
Ernest